Search the Community
Showing results for tags 'browser extensions'.
-
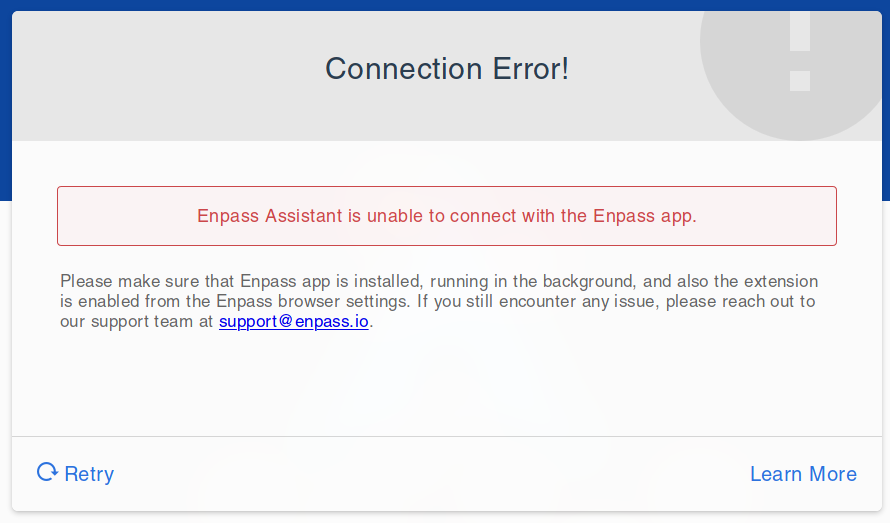
I have been using Enpass for a number of years now. However within the last few months (I can't pin it down more accurately than that, sorry), the browser extensions lose connection with Enpass after I suspend/sleep my computer. When I first boot in, the browser extensions work fine. If my computer is suspended and then woken, I get the below connection error. This happens with both Firefox and Chromium. Enpass does correctly pop up when the browser extension tries to connect but then it's like it can't see Enpass at all and eventually times out. I have tried restarting the browsers - no difference. Restarting Enpass - no difference. Restarting browser and Enpass doesn't work either. The only way I can get around it is by rebooting my computer (and making suspend pointless). Both Enpass and the browser extensions are up to date. I'm on Arch Linux (x86_64 Linux 5.3.13-arch1-1 kernel) with Deepin Desktop, Firefox 70.0.1 (and Chromium 78.0.3904.108).
- 3 replies
-
- linux
- browser extensions
-
(and 3 more)
Tagged with:
-
Hi Guys, i would prefer using the windows 10 and the browser extensions - without the desktop app. any idea when this will be possible? Thanks in advance Steffen
-
I recently came across this article: Password managers: attacks and defenses -- FEBRUARY 6, 2017 found here: https://blog.acolyer.org/2017/02/06/password-managers-attacks-and-defenses/. It describes common password attacks on password managers, mostly surrounding "autofill." For example, "The evil coffee shop attacker," "Sweep attacks," "Injection," and so forth. It lists several password managers like the big browsers (Chrome, Safari, etc.), Lastpass, 1Password, etc. It does not mention enpass. I would like to know if these types of autofill security concerns have been investigated and addressed in enpass. Thank you.