Search the Community
Showing results for tags 'audit'.
-
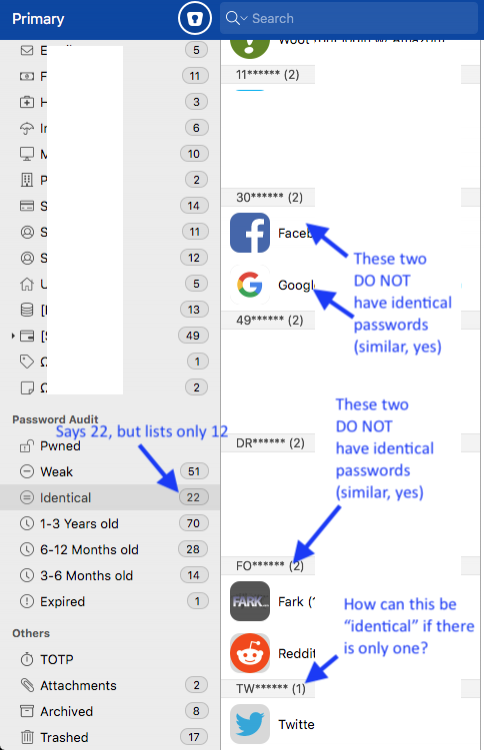
Beta 6.4.2 (667) I was poking around in Password Audit > Identical today and have run into a handful of issues: 1) If you're in All Vaults, the sidebar shows a count of "identical" passwords, but when you click on that category to view them, it's empty — the only way to see a list of identical passwords is to choose a particular vault first. 2) The count is inaccurate — in my primary vault, the sidebar shows 22 items, but only 12 appear in the list 3) Many of the items shown as identical are not identical — some of them are similar (the first 16 characters are the same, but last several characters are customized per site)... 4) ...but those first 16 characters are the same in a several of my passwords, so if bug #3 is because the app is (for some reason) only looking at the first XX characters in order to call them "identical," why did it only find 2 "matches"? 5) Of the 12 items shown, 2 of them are grouped all by themselves — listed as matching, but there are no matches. (And just to head off at the pass anyone who might want to admonish me for using passwords that have 16 characters in common, I have lots of entropy after those 16, and I'm in the process of randomizing all my passwords, but that takes time.)
-
Hello, I have a suggestion for Enpass that increases the security of passwords and alerts the user when a website was hacked and a password change is recommended. The password manager 1Password has a feature called watchtower. They have an internal database of security breaches (database with information about hacked websites where user-data was stolen). In this database they store the website and also the date of the breach. 1Password stores for password entries two modification dates: modification date of the password modification date of the entry 1Password checks the password entries against this database. When a website was hacked after the password was changed in 1Password, then 1Password recommends to change the password. When the password was changed after the hack of the website, then users get no notification. So when the entry for a page was last changed today (like added some notes), but the password itself was changed 2 years ago, then users get a warning when the website was hacked 2 weeks ago. For the password manager KeePass there is a plugin available called HaveIBeenPwned. The plugin and the source code are available here: https://github.com/andrew-schofield/keepass2-haveibeenpwned This plugin downloads the public breach lists form "'have i been pwned?" and from "Cloudbleed Checker". The plugin checks (on demand) your passwords against these lists. In KeePass there is no modification date of the password. To get the modification date of the password the plugin checks the history of each entry and compares the passwords (to find out the modification date of the password). Suggestion: Please add also such a feature in Enpass in the Password Audits. In my opinion it is OK if you use the public available lists from "'have i been pwned?" and from "Cloudbleed Checker" (like the KeePass Plugin). This requires that you also store the "password modification date". When you import entries from KeePass then you should also determine the password modification date of the entry. In the KeePass XML the complete history is also exported. Regards OLLI
-
Hello, I am using KeePass but I plan to switch to Enpass. One feature that I miss in Enpass is that in the password audit there is no option to find similar passwords. Means passwords that differ only in one or two characters. This would increase the security of Enpass a lot. Best regards OLLI