
Plexion
-
Posts
10 -
Joined
-
Last visited
Posts posted by Plexion
-
-
Hello is there anyone going to look into the issue above? Thanks.
-
2 hours ago, Anshu kumar said:
Hi @Plexion,
As mentioned by @Pratyush in the post above, it is the Windows itself which decides whether Enpass can be always unlocked using Windows Hello.
To determine whether your device have support Full-time Windows Hello, please have a look at these troubleshooting steps mentioned by @Garima Singh
Hope this helps!
Hi @Anshu kumar,
If you have read through my entire post, you will notice that I have gone through all 3 pages of this thread, and provided all the information your team has requested for throughout, including those highlighted in the link you have provided.
Kindly please check my previous post once again, for all the information requested, including the output from the test app. Windows Hello is said to be supported by the test app.
-
I am also having the same issue where Enpass will not unlock using Windows Hello after the first time it is started/restarted.
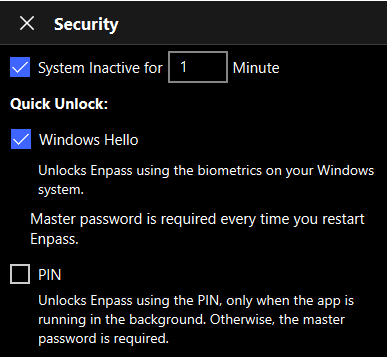
Enpass Security Screen
Below are my system details:
OS: Windows 10 Pro 20H2 19042.1052 x64 Enpass Version: 6.6.1 (804) from the Microsoft StoreSecurity Processor Details
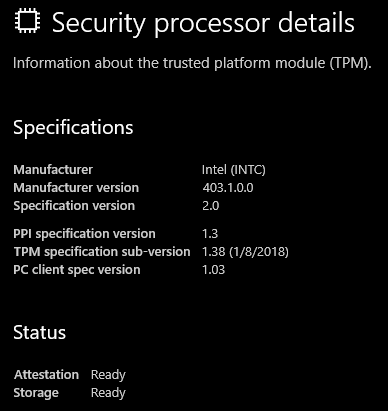
Get-TPM
TpmPresent : True TpmReady : True TpmEnabled : True TpmActivated : True TpmOwned : True RestartPending : True ManufacturerId : 1229870147 ManufacturerIdTxt : INTC ManufacturerVersion : 403.1.0.0 ManufacturerVersionFull20 : 403.1.0.0 ManagedAuthLevel : Full OwnerAuth : OwnerClearDisabled : False AutoProvisioning : Enabled LockedOut : False LockoutHealTime : 2 hours LockoutCount : 0 LockoutMax : 32 SelfTest : {}Get-TpmSupportedFeature -FeatureList "Key Attestation"
key attestationGet-TpmEndorsementKeyInfo
IsPresent : True PublicKey : System.Security.Cryptography.AsnEncodedData PublicKeyHash : ManufacturerCertificates : {} AdditionalCertificates : {[Subject] TPMVersion=id:00020000, TPMModel=CNL, TPMManufacturer=id:494E5443 [Issuer] CN=www.intel.com, OU=TPM EK intermediate for CNL_EPID_POST_B1LP_PROD_2 pid:9, O=Intel Corporation, L=Santa Clara, S=CA, C=US [Serial Number] **************************************** [Not Before] 13/2/2018 8:00:00 AM [Not After] 1/1/2050 7:59:59 AM [Thumbprint] **************************************** }Get-TpmEndorsementKeyInfo -Hash "Sha256"
IsPresent : True PublicKey : System.Security.Cryptography.AsnEncodedData PublicKeyHash : **************************************************************** ManufacturerCertificates : {} AdditionalCertificates : {[Subject] TPMVersion=id:00020000, TPMModel=CNL, TPMManufacturer=id:494E5443 [Issuer] CN=www.intel.com, OU=TPM EK intermediate for CNL_EPID_POST_B1LP_PROD_2 pid:9, O=Intel Corporation, L=Santa Clara, S=CA, C=US [Serial Number] **************************************** [Not Before] 13/2/2018 8:00:00 AM [Not After] 1/1/2050 7:59:59 AM [Thumbprint] **************************************** }Output from the WindowsAttestationTest_1.0.0.0_x86 App
21:33:38.4189779 HelloSupported::True 21:33:38.4239986 KCM::OpenStatus::NotFound 21:33:38.4259780 KCM::OpenFailed::RequestingCreate. 21:33:41.0279789 KeyRetrievalStatus::Success 21:33:43.1271809 GetAttestationStatus::Success 21:33:43.4383245 PublicKeySignStatus::Success 21:33:43.4383245 PublicKey::********************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************************Will you be able to assist please?
I have attempted the following but the issue still persists:
1. Clear the TPM both from Windows and the BIOS
2. Re-enroll Windows Hello.
3. Cleared Enpass data and restart from fresh.
Thank you.
-
Hi, any update please? It has been more than a month since this issue is raised here.
-
Hi @Garima Singh,
I am using the split tunneling feature by selecting only tunnel Microsoft Edge browser through the VPN.
I am including only the Microsoft Edge browser, and nothing else, which includes the Chrome browser that I am using Enpass on.
I am using Surfshark VPN on Windows 10.
Please let me know if you require more info.
Thank you.
-
Hi there,
It has been more than a month since the issue is submitted, are there any update for this issue?
It is quite frustrating needing to open the Enpass app manually and copy the credentials manually and fill it in webpages in Chrome.
Thank you.
-
Hi, may I know if there's any update please?
-
Thank you @Garima Singh, hope to hear from you soon.
-
Hi, I am using the Enpass Chrome Extension on Windows 10 2004 x64, with a VPN that has split-tunneling/application whitelisting feature, e.g. ProtonVPN, ExpressVPN, Surfshark, etc.
The Chrome extension is unable to connect to the Enpass desktop app whenever the split-tunneling feature is enabled in the VPN, even though the VPN is disconnected.
The logs just goes on and on like this:
- 11/2/2020, 9:23:36 PM : Connecting using websocket
- 11/2/2020, 9:23:36 PM : Opening connection on ws://127.0.0.1:10391
- 11/2/2020, 9:23:36 PM : Opening connection on ws://127.0.0.1:10392
- 11/2/2020, 9:23:36 PM : Opening connection on ws://127.0.0.1:10393
- 11/2/2020, 9:23:36 PM : Opening connection on ws://127.0.0.1:10394
- 11/2/2020, 9:23:36 PM : Opening connection on ws://127.0.0.1:10395
It is a hassle to turn the split-tunneling feature on and off each time I need to use Enpass.
I noticed that the Enpass extension works just fine in Microsoft Edge v86 (Chromium Edge), no matter if the extension is installed from the Chrome or Microsoft extension webstores.
Is there any way that it can be done to make the extension work in Chrome as well?
Thanks

Windows Hello doesn't work on system boot, must restart Enpass
in Windows 10 (Store)
Posted · Edited by Plexion
Not sure what change was introduced in the latest version, according to the change log, the browser inline autofill was added.
However, the Windows Hello feature is finally working as it should have been on version 6.7.4 (934) on Windows 10. You will need to disable and re-enable Windows Hello authentication in the Enpass app to achieve this.
Hope this will not be reversed in the future updates.