-
Posts
68 -
Joined
-
Last visited
-
Days Won
12
Everything posted by Fabian1
-
I have the impression that the Enpass team is sleeping. Almost nothing happens here. No bug fixes, no promised changes take place, no updates and no real improvements for a long time. The developers will only talk and that the fee will be collected every month... Some examples: Where are the common templates? Why I can't still create templates from entries? Why hasn't the bug with the ghost sections that cannot be deleted been fixed for more than 6 months? Why Enpass is working with a PIN after restarting my smartphone? 1Password requires the master password for security reasons. The Enpass team promised to change that months ago. Where is the option to use fingerprint and PIN at the same time? When will there finally be a new independent audit? This has been promised for more than a year! If you are also dissatisfied, please answer this complaint with "+1".
-
I have the impression that the Enpass team is sleeping. Almost nothing happens here. No bug fixes, no promised changes take place, no updates and no real improvements for a long time. The developers will only talk and that the fee will be collected every month... Some examples: Where are the common templates? Why I can't still create templates from entries? Why hasn't the bug with the ghost sections that cannot be deleted been fixed for more than 6 months? Why Enpass is working with a PIN after restarting my smartphone? 1Password requires the master password for security reasons. The Enpass team promised to change that months ago. Where is the option to use fingerprint and PIN at the same time? When will there finally be a new independent audit? This has been promised for more than a year! If you are also dissatisfied, please answer this complaint with "+1".
-
I have some "ghost"-fields in some items. There a sections and orders of fields shown, and when try to edit, they will disapear in edit mode, but stay in view mode. I posted this Error half a year ago. Nothing happens. The Enpass Team is sleeping, i guess. Only taking monthly money...
-
Whats about this and all the other problems??? Nothing happens here anymore. Only taking money monthly...
-
Dear SWFD, the sync of the vaults is independent from the licence. This are two complete different things. You have to enter your Email, if you install Enpass on a new device. But the sync depends of the cloud solution you use for you vault: Dopbox, etc. You could share a (extra) vault not only with your devices rather you could share it with friends and other people, if you want and need to. They don't need the same licence. The sync in your case will stop, if you would change the iCloud / AppleID-Account on one of your devices.
-
I am currently creating many templates. I got the idea that it would be nice if you could share it with other Enpass users. Is there a way to export or import the templates? Then everyone could publish their templates here in the forum and make them available to others. This would create a large template database for the Enpass community. It would also be great if you could create templates from existing entries. I have taken over a lot of entries from 1Password. I would like to make a template out of such an entry - of course without content.
- 1 reply
-
- 4
-

-
I have the same problem with the categories: 1. Categories that I have created in the past are not displayed in a new multiple vault. The checkbox in the category editing section is checked, but will not appear in the sidebar if only the new multiple vault is selected. I have created about 30 of my own categories and I would also like to use them in new Vaults. This is a real bug. 2. Entries that are moved / copied from one vault to another vault lose their category. I have to drag the entries back into the right category individually. It is very tedious and unnecessary work. In addition, I cannot see which category an entry is assigned to anywhere. Where can I see which entries are not yet assigned to a category? Why Enpass don't creates the category if it not exists in the vault, when the entry is copied / moved to this vault? Please answer.
-
You can also simply create a second vault and share it on all devices / with all users via the synchronization. the second vault of course needs the same password on all devices. But the password to unlock the app (and the default vault) can be different on every device. The logging could be realized via a protocol of the respective sync solution. Some cloud providers may allow multiple usernames and passwords, but they all access the same storage / account. Maybe by deleting individual users on the server, you could also exclude them from further synchronization, e.g. for lost devices.
-
Thank you for quick response.
-
Still no news to this questions?
- 18 replies
-
- ios
- masterpassword
-
(and 2 more)
Tagged with:
-
Still no answer to this very important question. Not a good sign to trust.
-
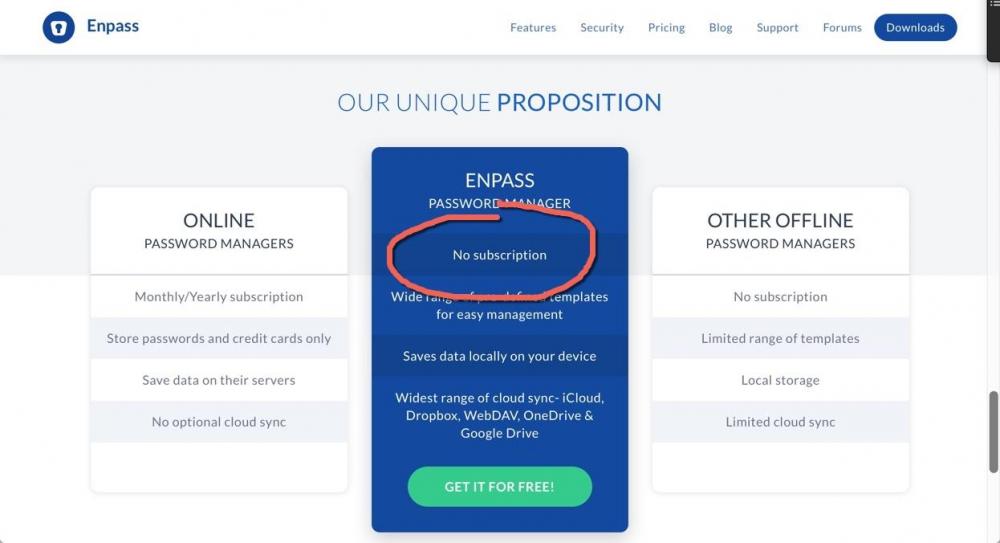
That is the point. I want to decide as a customer if and when to buy a new version (for example with new features). Subscription models hinder the development of the software. The developers do not have to win the customers again. You can see that in Adobe & Co. - since there subscription models were introduced, the software is only managed. Innovations take place elsewhere. Even though I now get a free lifelong access, I can not recommend Enpass anymore. What will it cost in the future? At least $ 1 a month - probably more. Future customers pay in one year, which had to be paid once. Before I discovered Enpass, I used 1Password for 10 years - and bought three new versions - also for my family. That cost a total of $ 150. With the new subscription model I would pay in this time $ 360 or even $ 600 (for a family account). And it's "only" a password safe. A relatively manageable piece of software. I have dozens of other programs on the smartphone and PC. If everyone wants $ 5 a month, that's more than $ 1,000 a year. Subscription models are money robbers. Dear Enpass Team, I would prefer that I have no free, lifelong access and instead Enpass would have a one-time purchase - even though you would have to pay more for new versions. You break your word! See it here - still on your website:
-
+1
-
I have some "ghost"-fields in some items. there a sections and orders of fields shown, and when try to edit, they will disapear in edit mode, but stay in view mode...
-
I really like enpass so much! But there is a fundamental security problem with the biometric unlock. face-id and fingerprint are not safe. you can hold someone's device in front of his face. or you press his finger on the device. We also leave fingerprints everywhere. They are even stored in many ID cards. this is a fundamental problem to unlock smartphones in this way and not a probem of enpass itself. but enpass should be more secure. its a pitty, that you need only seconds to overcoming the biometric unlock and all passwords are open! Enpass could become much safer with two very simple changes: 1. PIN & Biometric unlock at the same time. Please change the Enpass app so that the PIN and the biometric unlock are possible at the same time. Then a very short PIN could provide much more security. I would use a three-digit PIN and set the number of failed attempts to 1. After a single wrong entry, the master password must be entered. An attacker who overcomes the biometric unlock would thus only have a 1: 1000 chance. At the same time, the use of enpass remains very comfortable. 2. We urgently need a time-out for the biometric unlock. As in the desktop version, after a certain time (1 day) or when the device was restarted, the master password should always be queried. So it does 1Password - why not Enpass? It prevents attackers, who has captured the device from having all the time in the world to overcome the biometric unlock. Please implement this very simple features. You can set it by default to „only biometric unlock“ (without a pin at the same time) and set the biometric unlock timeout to „never“. So there will be no less comfort for people, that dont need higher security. kind regards Fabian
-
- 1
-

-
I can not remove the keyfile form a multi vault. there is no option do delete the keyfile on the "change password" section, as it is described in the manual.
-
I think, solve this problem is VERY EASY: just implement at button in enpass „sync now“. so the user can choose: syncing anytime at the background or only syncing at manual request.
-
I agree. The URL of some entrys in my vault is confidential. I dont want, that you at enpass knows all my server-domains...
-
You can create a travel mode yourself: Keep all important information only in an extra vault. The default vault contains nothing (or just passwords that you want to share with the border official ;-)) The extra vault should have a different password than your default vault. Do not store this password in your default vault (or delete it before traveling). Only this extra vault is synchronized with the cloud. Best with an anonymous webdav server, that can not be associated with you. The iCloud is not so good because it's tied to the Apple ID, that you can look up in the phone, so the border guard might ask for the Apple ID password, searching and finding your extra vault there and will ask for this password too. Also on all other devices (desktops, pads, telephones, etc.): the standard vault contains only a few unimportant passwords or remains completely empty. All devices synchronize the important data via cloud with the extra vault. If a device is to be taken over the border, then the extra vault and the sync with the cloud must be deleted. Only the standard vault - containing only unimportant passwords or fakes - remains on the device. After successful border crossing, the sync to the extra vault on the (secret) webdav server can be restored and the extra vault restored to the device. By the way, there is a big security advantage to synchronize all data only via an additional vault: The extra vault can be protected by a very complex password! It rarely needs to be entered, for example only after a border passage, when the sync is reestablished. A complex password protects the data, if the extra vault in the cloud should fall into the wrong hands. On the local device the password for the standard vault will also open the extra vault (unless it has just been deleted because of a border passage). The password for the default vault could be easier to type, because it is needed more frequently. And you can use different passwords for the default vault on any device. Some passwords easy to type on a desktop-pc are very unconfortable on a small iphone for example
-
another desirable change would be: the use of PIN and Biometric Unlock at the same time. That makes sense in the two-factor security philosophy: PIN - something you know. Finger or face - something you have. Biometric features alone are not safe, because unlocking can be done against the will of the user. For example, a border official would only have hold the iPhone in front of your face to unlock. And fingerprints are often stored on the border anyway. The combination of PIN and Biometric Unlock would also make very short PINs possible, maybe only two or three digits. That would be very comfortable. And ih would be very safe, because someone who looked over the shoulder while unlocking, could not do anything with it, because he lacks the biometric part.
- 18 replies
-
- ios
- masterpassword
-
(and 2 more)
Tagged with:
-
very good
- 18 replies
-
- ios
- masterpassword
-
(and 2 more)
Tagged with:
-
Dear Enpass Team, do you plan an audit for ios? Best regards.